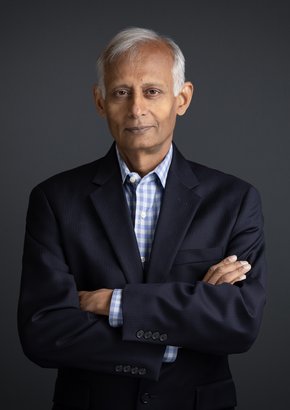
Brenda McCulloch
CSIO
While working remotely has freed huge swathes of the global population from the drudgery of daily commutes to the office, it has also resulted in data leaks, hacks and cybersecurity devastation for a large number of organizations.
Companies that hold sensitive information have been especially vulnerable to attack. And for many, 2020 resulted in the worst hacking and breach incidents on record.
Brenda McCulloch, Chief Information Security Officer (CISO) for Teranet, is responsible for the cyber fortification at Canada's leading delivery and transformation of statutory registry services. As a provider of extensive expertise in land and commercial registries, data - and the protection of it, is paramount to its success.
McCulloch’s 20-year career in the IT industry stands her in good stead, and she believes an organized team, careful prep work, and properly allocated expertise and resources are the keys to making sure companies maintain their security correctly in these challenging times.
“It’s always about balance,” she says, with a hint of zen. “Ultimately, it’s risk versus reward. What you want to achieve out of a security programme and what you want to invest, versus what kind of exposures and risks that organization faces.
“My past roles include positions where I was internally facing and externally facing, so I have consulting experience as well as building an inhouse security practice from scratch.
“From those two experiences and perspectives, I have built a very balanced view of different ways to deliver a security protocol to different companies.
Zero Trust security
Teranet is developing a zero-trust security architecture. This multi-layered solution that prevents and slows down the damage that can be wrought in a major breach has been instrumental in fortifying the company’s cyber strategy.
McCulloch uses an analogy to describe exactly how the system works. “So, in terms of a home, you’ve got the doors to your house and there are keys to the door. In a traditional security model, you protect the doors of the home. You lock the doors to ensure no security breach occurs. You use a strong lock and you make sure only certain people have keys to the lock.”
As part of her work at Teranet, McCulloch has also been instrumental in building a security practice programme and team. The challenges involved in such a project often hinge on resources and executive-level approval.
“You’ve got to make sure the executives at the organization are mindful of the endgame - because the endgame is where they believe that investment must go - and a lot of the time the endgame is where the risk appetite ends.
McCulloch says that very often, root cause of a breach stems from weaknesses in operational activities or security hygiene.
“I think many of the root causes of many recent breaches were because companies have repurposed some of the operational as well as the security hygiene resources to new initiatives.
“I think it's really important that when you augment new initiatives, that you also augment the resources at the same time,” she says.
Ultimately, says McCulloch, if companies have low investment but high-risk weakness items, that's something they should address.
Read the full story HERE

Featured Interviews
“It's very different recruiting people for something you're building from scratch, compared to recruiting for something that is already running.”